What is Symbiotic?
Symbiotic is a shared security protocol designed as a coordination layer that allows network builders to control and customize their (re)staking implementations in a permissionless manner. It provides flexibility, risk minimization, and capital efficiency through a combination of its modular components and core principles.
Key Benefits of Symbiotic:
- Flexibility through Modularity: Networks have full control over their (re)staking implementations, including decisions on collateral assets, node operator selection, rewards, slashing, and resolution mechanisms. Participants can choose to opt in and out of shared security arrangements.
- Risk Minimization through Immutability: The core contracts are non-upgradeable and deployed on Ethereum, which mitigates external governance risks and eliminates single points of failure. The protocol's design focuses on minimizing execution layer risks.
- Capital Efficiency through Restaked Collateral and Reputation-Based Curation: The protocol is permissionless, multi-asset, and network-agnostic, which supports scalable and capital-efficient economic security sourcing. It includes a reputation system for operators that enhances capital efficiency for network builders.
Components of the Symbiotic Protocol:
- Collateral: Represents underlying on-chain assets and is chain- and asset-agnostic. Can include ERC20 tokens, Ethereum validator withdrawal credentials, or other on-chain assets like LP positions.
- Vaults: Manage the delegation of collateral to operators across networks. Vaults can be curated by liquid (re)staking providers or institutional holders, or through operator-specific delegations.
- Operators: Entities that run infrastructure for networks (validators, sequencers, guardians, keepers, etc.). Symbiotic maintains a registry of operators, allowing them to opt into networks and receive economic backing from restakers through vaults.
- Resolvers: Entities or contracts that handle the passing or vetoing of slashing penalties incurred by operators. Agreed upon by vaults and the networks they provide security for, resolvers can be automated or take the form of committees or external frameworks.
- Networks: Protocols requiring distributed node operators for trust-minimized services like decentralized transaction sequencing, consensus on off-chain data, oracle services, and more. Symbiotic allows network builders to define, control, and adapt methods for onboarding, incentivizing, and penalizing operators and their delegators.
The Symbiotic Architecture
Symbiotic's contracts architecture balances security, flexibility, and accessibility. The architecture outlines the upgradability and accessibility of various contract components, ensuring a robust and adaptable framework for network builders and participants.
Upgradability:
- Immutable Contracts: These contracts cannot be upgraded once deployed. They ensure a high level of security by eliminating the risk of changes or tampering after deployment. Core contracts on Ethereum are typically immutable to remove external governance risks and single points of failure.
- Migratable Contracts: These contracts can be upgraded by their owners to newer versions provided by their factory. This allows for improvements and adjustments over time without disrupting the existing system. Vault contracts that need periodic updates for optimization or to incorporate new features.
- Not Specified Contracts: The upgradability of these contracts is not predefined, meaning they may or may not be upgradeable depending on the specific implementation. Certain utility contracts whose upgrade status depends on their deployment context and necessity.
Accessibility:
- VaultFactory: The VaultFactory contract is ownable, meaning it has an owner who can manage specific administrative functions. The owner can whitelist new Vault implementations, ensuring that only approved and vetted Vaults are deployed.
- Vault: The Vault contract is ownable, allowing it to migrate to newer versions when necessary. Vaults use a roles-based access control mechanism, providing granular control over who can perform specific functions. This ensures that only authorized entities can execute critical operations.
- Collateral and Rewards Distributor: These components can have any level of accessibility, depending on their specific roles and the security requirements of the network. The flexibility in accessibility allows these contracts to be tailored to the needs of different projects, ensuring the right balance between security and operational efficiency.
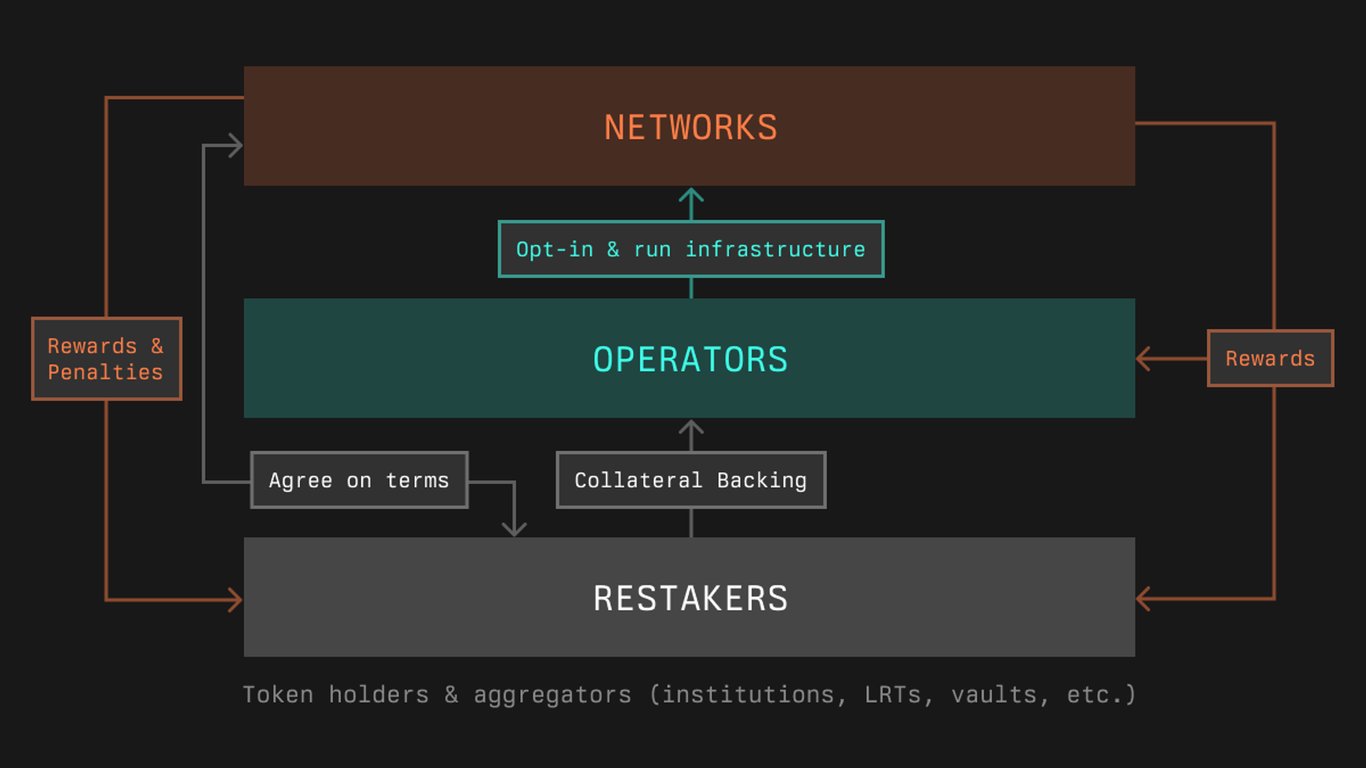
How Does Restaking Work on Symbiotic?
Restaking on Symbiotic enables projects to source operators and scale economic security for their decentralized networks. Here’s a detailed overview of the process:
- Project Integration: Various decentralized projects, including appchains, DA (data availability), MEV (miner extractable value), rollups, bridges, and more, integrate with the Symbiotic protocol to leverage its shared security model.
- Collateral Provision: Participants, known as restakers, provide collateral. This collateral can be in the form of ERC20 tokens, Ethereum validator withdrawal credentials, or other on-chain assets. The collateral serves as the economic foundation that supports the security and operations of the network.
- Vault Creation: Vaults are created to manage the pooled collateral. These vaults can be managed by liquid (re)staking providers or institutional holders.
- Operator Selection: Symbiotic maintains a registry of operators, such as validators, sequencers, guardians, and keepers. These operators opt into the networks that require their services and receive economic backing from the restakers through the vaults. Operators are selected based on their reputation and performance across various networks, ensuring reliable service.
- Economic Security Scaling: By restaking their assets, restakers help scale the economic security of the networks. The permissionless, multi-asset, and network-agnostic design of Symbiotic supports scalable and efficient economic security sourcing, enhancing network resilience.
- Reputation-Based Curation: Symbiotic employs a cross-network reputation system for operators, which further enhances capital efficiency. Operators build their reputation based on performance, which helps in curating and selecting reliable operators for different projects.
- Risk Management and Dispute Resolution: Resolvers are implemented to handle slashing penalties or disputes arising from the operators' activities. These resolvers can be automated systems or take the form of committees or external dispute resolution frameworks, providing a neutral third party to arbitrate penalties.
Application Across Different Projects:
- Ethereum: Projects on Ethereum use Symbiotic to add extra security layers and efficiently restake assets.
- Appchains: Application-specific blockchains (appchains) integrate Symbiotic to source reliable operators and secure their networks.
- Data Availability (DA): DA layers utilize Symbiotic to ensure secure data storage and retrieval by incentivizing operators with staked collateral.
- Miner Extractable Value (MEV): MEV projects leverage Symbiotic to manage and distribute rewards among operators while mitigating centralization risks.
- Rollups: Rollup networks enhance their security and decentralization by using Symbiotic to manage operator selection and restaking assets.
- Bridges: Cross-chain bridges secure their operations by utilizing Symbiotic to restake collateral and source reputable operators.