What is Pell Network?
Pell Network is a decentralized token economy security leasing platform designed to bolster the Bitcoin ecosystem by aggregating native BTC stake and LSD (Liquid Staking Derivatives) restake services. Its core objective is to extend cryptographic economic security across a range of Bitcoin-based protocols, applications, and infrastructure, particularly focusing on Bitcoin Layer-2 (L2) networks.
Addressing Ecosystem Challenges
- High Bootstrapping Costs: Establishing new trust networks for each module can be costly. Pell Network's unified security model mitigates these costs, allowing developers to quickly and efficiently deploy new decentralized validation modules.
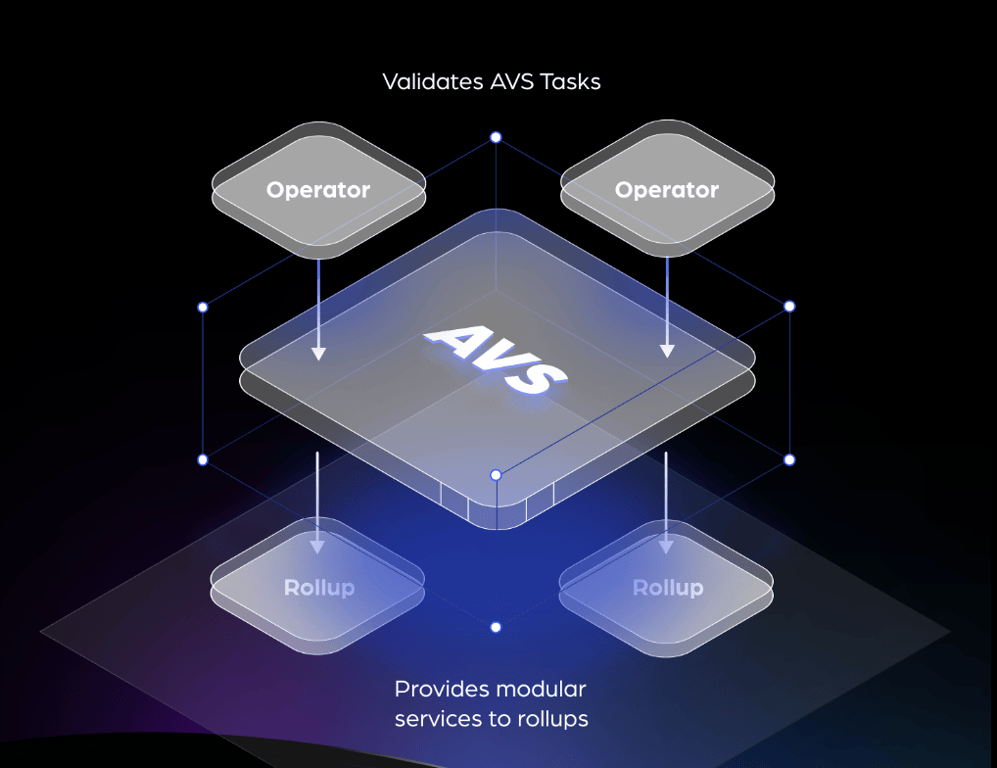
- Economic Efficiency: The platform aggregates Bitcoin's security across all modules, enhancing overall security while providing cost-effective solutions. This approach reduces the burden of capital costs associated with staking, which often exceed operational costs in other AVSs (Actively Validated Services).
- Support for Bitcoin Layer-2 Networks: By optimizing components like data availability layers and RPC nodes, Pell Network aids in constructing robust and efficient Bitcoin Layer-2 networks, ultimately improving user experience and network performance.
Key Features and Components
- Decentralized Security Leasing: Pell Network aggregates Bitcoin's native security for various modules, providing a unified security layer that enhances the security of decentralized applications (dApps). This avoids the fragmentation of security resources and value flow that would otherwise occur if each module maintained its own trust network.
- Multi-Layered Service Network: The platform offers a broad spectrum of services, including validation for consensus protocols, data availability layers, virtual machines, guardian networks, oracle networks, bridges, threshold encryption schemes, and trusted execution environments. By consolidating security, Pell Network allows for more efficient and cost-effective deployment of these services.
- Staking and Investment Opportunities: Pell Network provides diverse staking options, enabling ecosystem participants to contribute to and benefit from the network's security. This not only incentivizes participation but also helps develop an economic circulation system within the Bitcoin ecosystem.
- Support for Advanced Technologies: The network plans to integrate advanced technologies like machine learning, AI, and GPU computing power, expanding the scope of applications and improving overall performance.
- Critical Infrastructure Security: Pell Network aims to provide economically efficient security solutions for critical infrastructure components, such as oracles and cross-chain bridges. This is crucial for maintaining the integrity and efficiency of the broader Bitcoin network.
The Pell Network Architecture
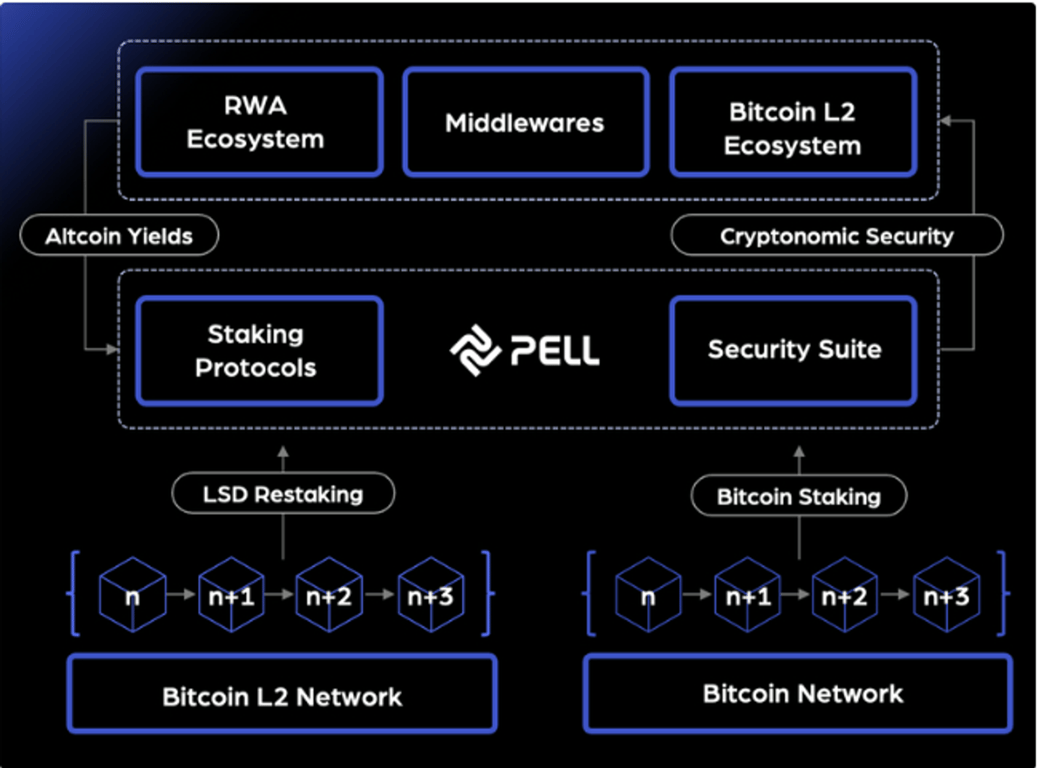
The Pell Network Architecture is designed to provide a comprehensive and secure platform for the Bitcoin ecosystem, particularly focusing on Bitcoin Layer-2 (L2) networks and other decentralized services. The architecture comprises several key components and layers, each playing a crucial role in maintaining the network's integrity and efficiency.
Key Components
- RWA Ecosystem, Middlewares, and Bitcoin L2 Ecosystem: These layers represent various applications and protocols that utilize the Pell Network for enhanced cryptonomic security. They include real-world assets (RWA), middleware services, and Bitcoin L2 solutions.
- Altcoin Yields: The network facilitates generating yields from altcoins, providing additional financial incentives for participants.
- Staking Protocols: Pell Network allows users to participate in staking, either through LSD (Liquidity Staking Derivatives) restaking or direct Bitcoin staking. This staking supports the security and validation of various services and protocols within the network.
- Security Suite: A set of tools and mechanisms ensuring the security and integrity of the network, including cryptoeconomic measures to deter malicious activities.
- LSD Restaking & Bitcoin Staking: Participants can restake their assets, including LSDs, to secure the network and validate transactions. This staking mechanism supports both Bitcoin and L2 networks, contributing to the overall security and functionality of the ecosystem.
- Bitcoin L2 Network & Bitcoin Network: The architecture supports various nodes (n+1, n+2, n+3, etc.) that collectively maintain the network's security and operational efficiency. The distinction between the Bitcoin L2 Network and the Bitcoin Network indicates the system's capability to handle transactions and services across different layers of the Bitcoin protocol.
Network Structure
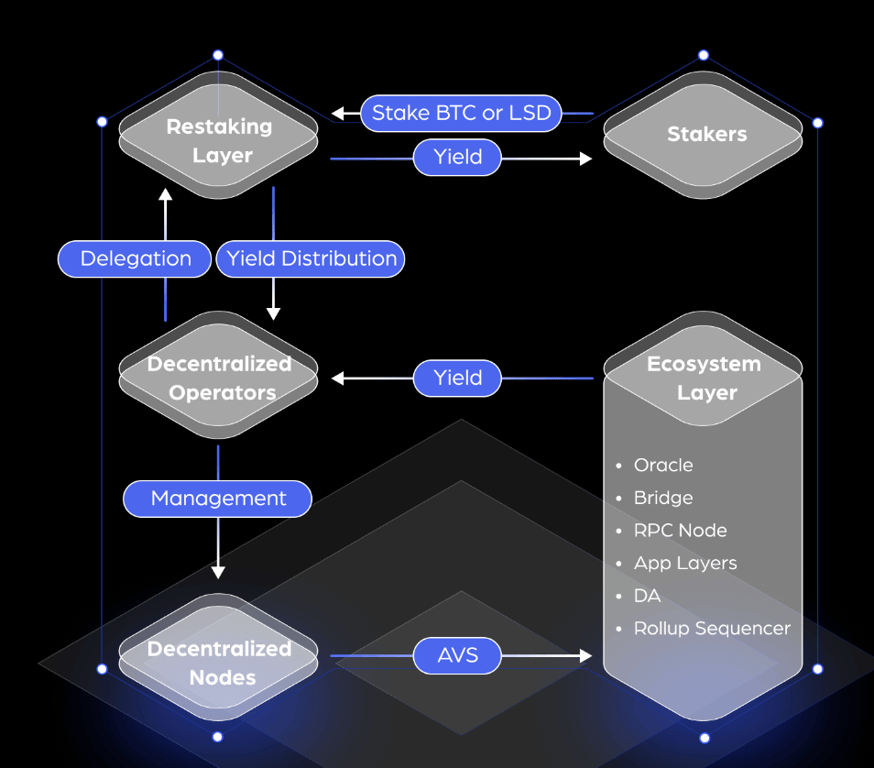
How does Restaking Work on Pell Network?
Pell Network offers a versatile restaking mechanism that allows stakers to earn additional income by participating in various services across different blockchain layers.
Restaking Mechanisms
- Native Restaking: Validators can restake their BTC by redirecting their withdrawal credentials to Pell Network contracts. This effectively integrates Bitcoin staking into Pell Network, enhancing security for new services and providing revenue-stacking opportunities.
- LSD Restaking: Stakers can restake their Liquid Staking Derivatives (LSD) of BTC through Pell Network smart contracts. This mechanism enables users to stack DeFi earnings by transitioning from other protocols into Pell Network, expanding the potential use cases for their assets.
- BTC LP Restaking: This involves staking LP tokens that contain BTC, allowing users to contribute liquidity to the network while securing additional services and earning returns.
- LSD LP Restaking: Similar to BTC LP Restaking but specifically involves LP tokens containing liquidity staked BTC tokens. This approach allows for an extended revenue stack from Bitcoin to DeFi and into Pell Network.
Staking Modes
- Independent Staking: Stakers can directly opt-in to validate Actively Validated Services (AVSs) on Pell Network, participating in the network's security and earning rewards.
- Delegation: Stakers can delegate their assets to Pell Network node operators who manage the technical aspects of validation. Delegators earn a share of the fees collected by the operators, who retain a portion as compensation for their services.
Delegation Mechanism
- Trust and Due Diligence: Delegators must carefully choose trustworthy operators, as any failure in fulfilling obligations can lead to slashing, affecting both the operators and the delegators' staked assets.
- Fee Distribution: Operators create delegation contracts specifying the fee-sharing arrangements, creating a competitive market for delegations within Pell Network.
Slashing Mechanism
- Cost of Corruption (CoC): Pell Network imposes stringent slashing rules to ensure high cryptoeconomic security. If a validator is found engaging in malicious activities, their staked assets can be slashed, ensuring the integrity of the network.
- Non-Fungible Tokenization: Due to the varying risks associated with different AVS modules, Pell Network does not issue fungible tokens for restaked positions. Instead, unique tokens are issued, reflecting the specific risks and rewards of each staker's involvement.
Integrated LRTfi Projects, AVSs and Operators on Pell Network